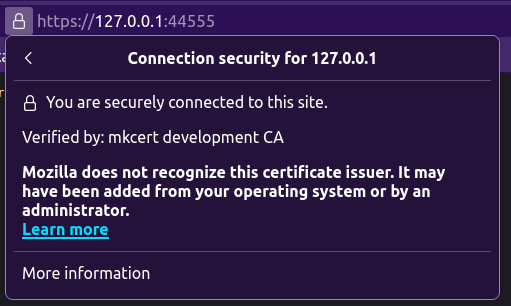
Develop using HTTPS¶
To develop locally with HTTPS using a trusted certificate, it is recommended to
use mkcert, which is a simple tool
for making locally-trusted development certificates.
- Install
mkcert - Install the root certificates authority (CA) using the
mkcert --installcommand - Generate a certificate for local development using the command:
mkcert localhost 127.0.0.1 ::1 - Use the feature of the
ASGIserver you select, to run with HTTPS. Foruvicorn, refer to this documentation: https://www.uvicorn.org/deployment/#running-with-https.
Example:
mkcert --install
mkcert localhost 127.0.0.1 ::1
uvicorn server:app --port 44555 --ssl-keyfile=./localhost-key.pem --ssl-certfile=./localhost.pem
Last modified on: 2025-04-01 23:22:49
RP